- What We Do
- Operate
- Services
- Cyber Resilience Services
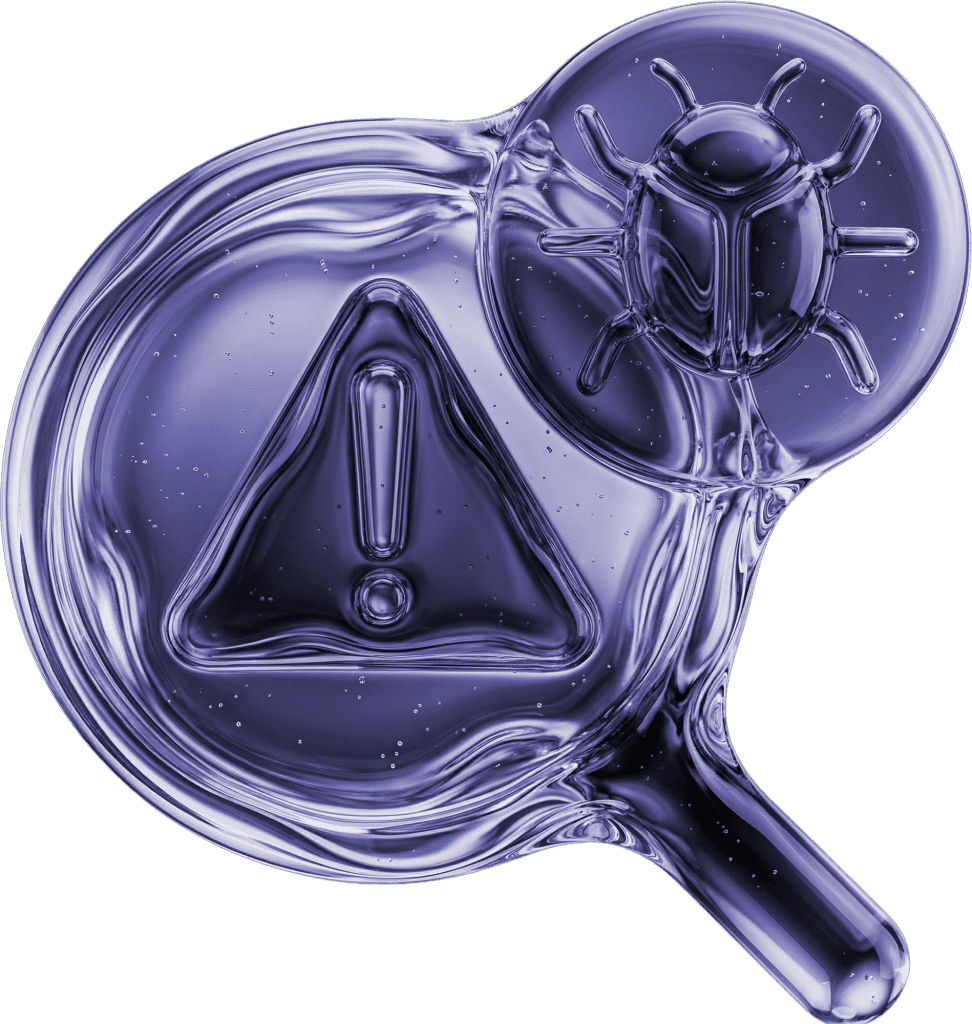
- Cyber Threat Exposure Management (CTEM)
Cyber Threat
Exposure Management
(CTEM)
Prove your controls work against attacks.
Identify, test, and prioritize exposure across your environment to ensure your security controls work as intended. Move beyond static assessments to continuous, risk-based validation.
ALWAYS
ON GUARD
Continuous control validation
Test defenses against
real-world attack techniques
safely and continuously.
Exposure analysis
Identify how vulnerabilities
and misconfigurations combine
into exploitable paths.
Risk-based prioritization
Focus remediation on the exposures
attackers are most likely to exploit.
Benefits
Full exposure visibility
Understand real attack paths across your environment.
Reduced risk over time
Continuously validate and close critical gaps.
Evidence-based assurance
Demonstrate control effectiveness to leadership and regulators.
Ready?
Let's talk.
LATEST